A good start means a great deal.
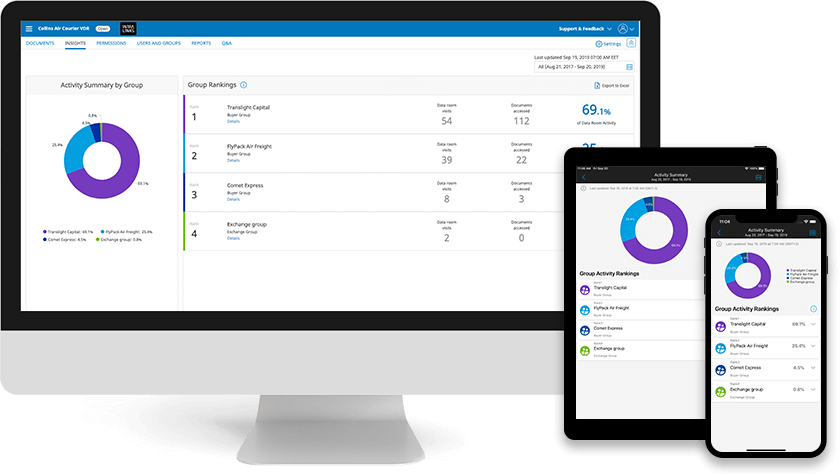
Accelerate your deal with Intralinks Virtual Data Room
- Upload deal docs right away
- Pay only if your deal moves forward
- Use AI-powered due diligence tools
- Maximize deal security and privacy*
*Intralinks is the only VDR provider to achieve industry’s highest privacy standard: ISO 27701 certification.
What’s new at Intralinks
More than two decades after pioneering the virtual data room, we’re still the leading innovator in financial technology.
Preferred by dealmakers everywhere.
See what’s new in our pioneering virtual data room and why we are the first in the market, year after year.
Safer.
Share with confidence and compliance.
Simpler.
Focus on your deal, not the technology.
Smarter.
Save time and avoid costly errors.
Intralinks Dedicated Services Group
Expert help, with a personal touch. On call any time, any place, in 140 languages.
You're in good company.
4.1 million+
10,000+ M&A deals
$34.7 trillion worth
As bankers, we understand the care that must go into sharing confidential documents. With Intralinks, there’s only one source to check no matter how many documents there are. That makes it easier to maintain security and control, so we don’t have to worry about security breaches or people sharing documents inappropriately.
INSIGHTS
Must-read thought leadership, networking opportunities and leadership tools.













