Boost Data Security, Privacy & Compliance with Intralinks
Used by the most regulated industries to share high-value, high-risk information.
Security is at the heart of everything we do. It maintains the integrity of our products, fuels our mission, inspires our personnel and protects our hard-earned reputation.
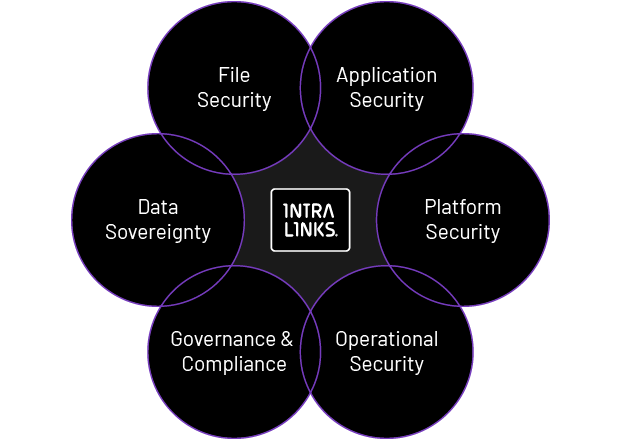
Our security model is comprised of six disciplines and technologies that include data sovereignty, governance and compliance, and four security levels: file, application, platform and operations. Together, they provide our clients with the processes, controls and reporting required to safeguard their data and operations while exceeding regulations and reducing risk.
Find out how Intralinks can keep your data safe, so you can stay productive.
Features
Data privacy and sovereignty
Intralinks has a comprehensive approach to data sovereignty designed to meet regional requirements. Based on the Intralinks Trust Perimeter™, our capabilities and disciplines include:
- Distributed Content Nodes - Distributed architecture to enable in-region data storage and processing, ensuring content never physically leaves a specified region
- Intralinks UNshare® - Information rights management that protects local or remotely shared files and other sensitive information from unauthorized access
- Legal Avenues - Optionality in its approach to global regulations surrounding data transfers, including EU-US Privacy Shield and Standard Contractual Clauses
- Audit, Reporting, Compliance - Comprehensive audit and reporting to provide full audit trails of all user activity with the appropriate context for regulatory enquiries physical audit to allow our customers to verify our high standards
Learn more about our approach to data privacy and sovereignty.
Governance, risk and compliance
Intralinks provides a comprehensive set of tools and assistance to support our customers in their governance and compliance journey, including:
- Compliance Logging - Full tracking and event capabilities on all access and controlled document changes and activities
- Compliance Reporting – Diverse standard reporting capabilities designed for industries where compliance is required as well as the ability to provide a series of custom reports; flexible compliance reporting feeds are also available for integration with customer systems
- Governance Extensions – Fully enhance and customize business applications to extend IT governance and control over them; manage the full VDR lifecycle of workspaces to order, provision, run, retire and archive them


Platform security.
Our platform-level security features encrypt and protect data at rest, in transit and in use. They also provide reporting and analytics, and enable organizations to control storage architecture to comply with GDPR and other data privacy regulations.
- Comprehensive audit reports and analytics for regulated and non-regulated industries
- Compliance with data privacy laws enabled by distributed content node architecture
- Extension of existing enterprise security technologies to maximize ROI
- Global storage network to enable compliance with regional data sovereignty requirements
File security.
Unless your information is locked at the file level, every email sent by your employees has the potential to cause a security breach. Intralinks automatically encrypts and embeds file-level security in every document to give you control over who can open a file, what can be done with it, and how long it is accessible.
- Easy-to-manage file protection inside or outside your firewall
- One-click to enable and one-click to retract access to a document with Intralinks UNshare
- No plugins required
- Dynamic watermarking to label printed documents and flag them confidential
- Advanced encryption standards provide multi-tier key management protection
- Master key with random 256-bit encryption key per file protects unique data keys
- Separation of duties protects master key from system and database administrators
- Unique data-encryption keys for each client

Application security.
Additional application security capabilities restrict information access based on group, individual and device. They also maintain audit trails and control sign-in requirements.
- Configurable control of file, folder and workspace access by group, user and device
- Team resource management facilitated by assignable roles
- Full audit trails with real-time status and detailed compliance reports
- Control of specific application functionality, such as local file sync and mobile device access
- Risk-based multifactor rules engine
- Data-driven authentication rules
- Channel-driven single sign-on (SSO)
Operational security.
Intralinks employs a robust set of processes and personnel procedures to protect our network infrastructure, physical storage facilities and client data.
- Infrastructure security includes geographically dispersed datacenters; 24x7 facility security; intrusion detection; fault-tolerant architecture; DDoS protection and web application firewall; and secure DNS/website cloaking
- Personnel security requires extensive employee and contractor background checks and strictly enforced confidentiality agreements
- Process security includes user ID dissemination, robust and auditable change controls, a detailed business continuity plan and BSIMM process
- Dedicated compliance team manages assurance programs for onsite customer audits, external compliance, security reviews of facilities and processes, code and architecture reviews and other activities

Audits and certifications.
Since 2014, Intralinks has passed over 280 client-led audits of our physical data centers, source code, processes, applications and personnel management. We hold ISO 27001 and industry-specific certifications.
Want to learn how we can benefit you?