Our security.
Your trust.
Intralinks’ security features protect your deal and data through an ecosystem that’s focused on security for you, your customers and your partners.

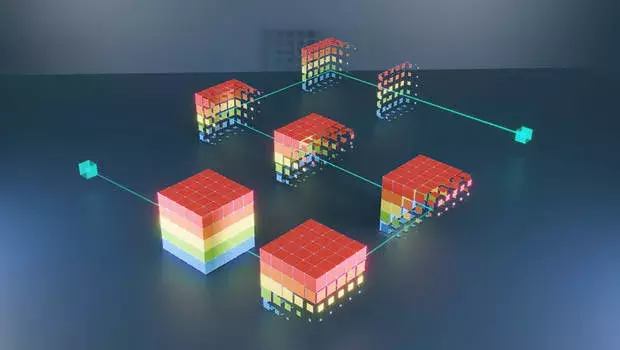
Our Intralinks Trust Perimeter™ gives you integrated, multi-layer security and compliance.
Document Security
Complete Control
- Easy-to-manage file protection inside or outside your
firewall - One-click document access or retraction with Intralinks UNshare™
No Plugins
- Built-in security that does not require plugins or added technology to manage
- Automatic file-level embedding and encryption security in every document
Advanced Encryption and Dynamic Watermarking
- Easily label printed documents and mark as confidential
- FIPS 197 standard encryption with multi-tier, AES-256 key management protection
Application Security
Fully Configurable
- Custom file, folder and workspace access control by user, group and device
- Monitor specific application functionality, including mobile device access control
Robust Authentication Engine
- Risk-based, data-driven multifactor authentication (MFA) engine with channel-driven single sign-on (SSO)
- Enhanced login and authentication with Intralinks Identity Services for even greater protection and control
Simplified Compliance
- Full audit trails with real-time status
- Detailed compliance reporting to reduce risk
Platform Security
Always Protected
- Encrypts data at every stage — at rest, in transit and in use — plus reporting and analytics
- First VDR provider to achieve ISO 27701 certification —the highest standard in data privacy
Global Network
- Compliance with data privacy laws, like GDPR, through distributed content node architecture
- Global storage network enables compliance with regional data sovereignty requirements
Flexible Application
- Comprehensive audit reports and analytics for regulated and non-regulated industries
- Extension of existing enterprise security technologies to maximize ROI
Operational Security
Robust Document Sharing Trust Protocols
- Designed to protect our network infrastructure, physical storage facilities and client data
- Geographically dispersed data centers, 24x7 facility security; fault-tolerant architecture, DDoS protection, web app firewall, secure DNS/website cloaking
Secure Internal Procedures
- High-level employee and contractor background checks with strictly enforced confidentiality agreements
- User ID dissemination, robust and auditable change controls, business continuity plan, BSIMM process
Dedicated Compliance Team
- Ensures around the clock protection, 24/7/365
- Manages customer requests for onsite audits, external compliance reviews and security assessments of facilities, code and architecture
World-class security

Data privacy
and sovereignty
Intralinks complies with the E.U.-U.S. Data Privacy Framework (E.U.-U.S. DPF) and certifies that it adheres to the E.U.-U.S. Data Privacy Framework Principles (Principles).
The Principles govern in the event of any conflict between the Principles and the Privacy Policy. For additional info: https://www.dataprivacyframework.gov/
In-Region Processing Storage
Flexible architecture that enables in-region data storage and processing, ensuring content never physically leaves a regulated region
Intralinks UNshare®
Information rights management (IRM) that protects local or remotely shared files and other sensitive information from unauthorized access — even after it's downloaded
The Intralinks Trust Perimeter™
Customers can “define their own perimeter” to meet regional and global data protection standards as information security and compliance needs change
Legal Avenues
Adaptable to geo-specific regulations for data transfers, including the E.U.-U.S. Data Privacy Framework (E.U.-U.S. DPF) and Standard Contractual Clauses
Audits, Reporting and Compliance
Full audit trails of all user activity, with appropriate contexts for both regulatory inquiries and physical audits by our customers to validate our high standards
Governance, Risk and Compliance
Intralinks offers a diverse set of tools and assistance to support our customers’ ongoing compliance and governance journeys.
Compliance Logging
Enables full tracking and event capabilities on all access and controlled document changes and activities
Compliance Reporting
Provides an array of standard and custom compliance reporting capabilities, with available flexible compliance reporting feeds for customer system integration
Governance Extensions
Manages the full lifecycle of VDR workspaces, including order, provision, run, retire and archive applications by consolidating business applications under IT governance and control